EDIT: keep the publish date in mind before reading lol
Pretty much everyone I’ve talked to about Chromebooks has either really resonated with the good things I say about them, or the other, much larger group, will look at me like I’ve started to speak an alien language.
Hopefully with this post I’ll do my part to take away from the stigma that Chromebooks are only good for kids in grade school.
Linux
First off, I want to touch on one of the largest misconceptions that is still tossed around about Chromebooks today. That being, you can only do things on a Chromebook that you can do in your browser.
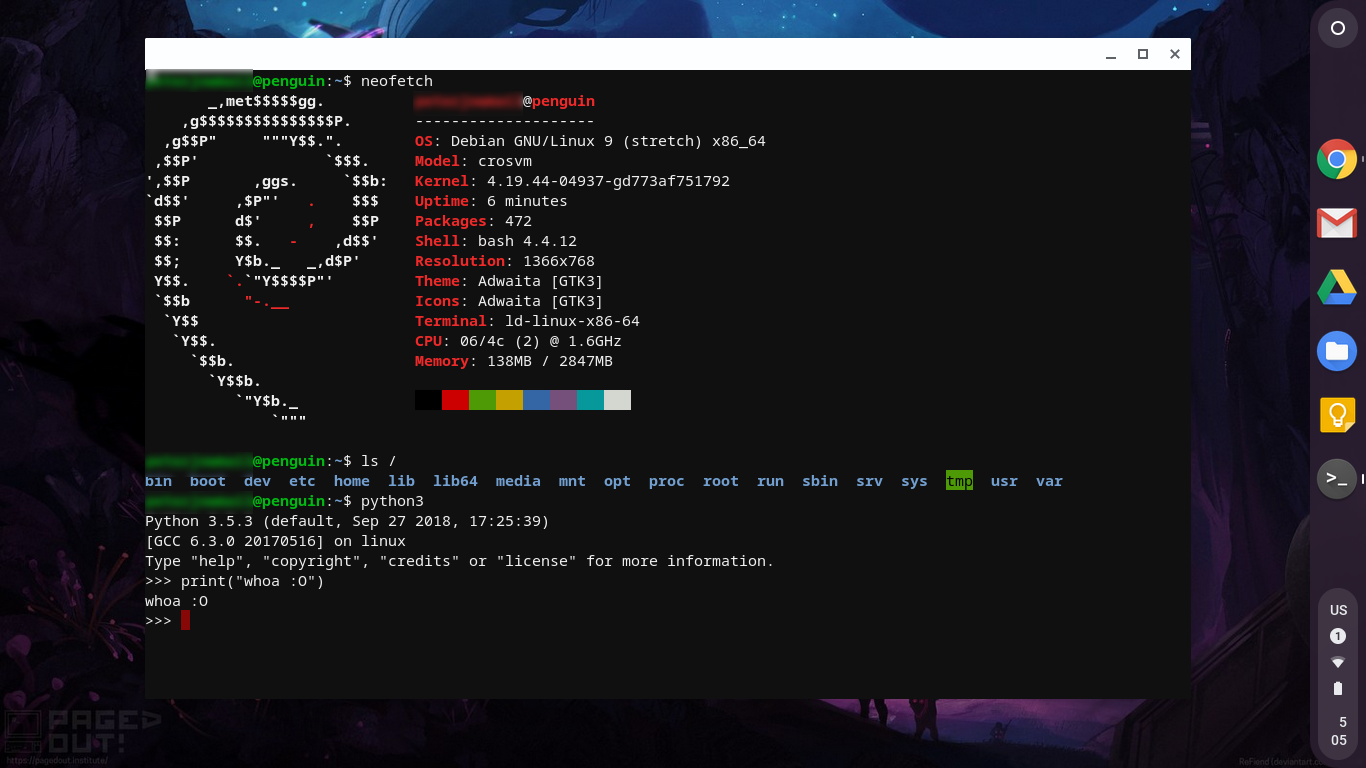
This hasn’t been true for quite a long time, Android apps were introduced in 2016, and more notably, you can now easily get a full Linux VM using Crostini, and install programs like vscode easily with apt. As you might imagine, with a full VM you can actually do some real development work without straying too far from your usual workflow.
To access this you do need Chrome OS version 69 (nice) or higher, and your device should be on this list of confirmed working devices:
The sandboxing section of this post covers in a bit more detail how the VM is separated from the host.
Affordability
Probably the most obvious point, but still very important, is affordability. You can get a decent Chromebook for just a few hundred $ (I’ve been running a $250 CAD Chromebook for about a year with pretty much no complaints except the really weird keyboard layout
(Really, who at Acer thought that really tiny shift keys paired with no caps lock was a good idea??)
While affordability is a great part of Chromebooks, there are some high end (>$1000) models out there, such as the Google Pixelbook if that better suits your needs. But personally, I prefer the feeling of having a device I don’t care too much about if something happens to it.
Security
This is a big, and in my opinion the most enticing “feature”. There’s a lot to go over so I’ll split it up into multiple sections.
If you do just want the generalizations, check out Google’s security overview here
Verified Boot
Each time you start up your Chromebook, it goes into a process called “verified boot”, which checks to make sure that there have been no alterations to your machine before booting.
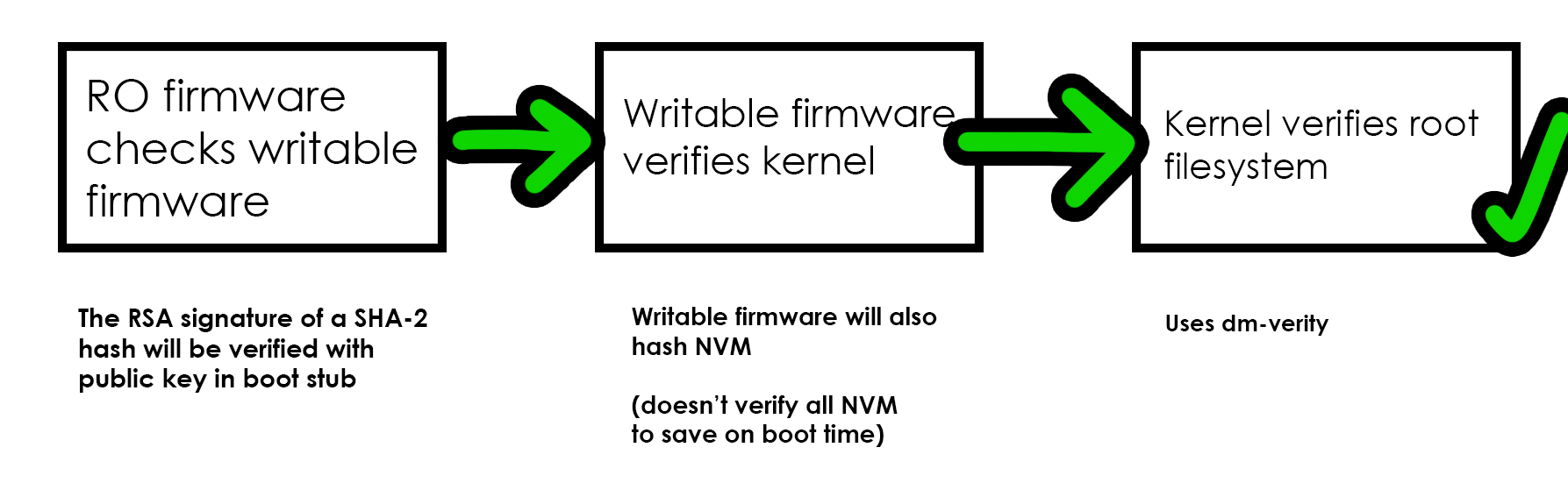
Above I’ve illustrated* an extremely simplified version of Chrome OS’s verified boot. As you can see, each subsequent piece relies on the previous one to verify if it is valid. If it at any point is not, it will go into the recovery process and warn the user. More on the recovery process here
NOTE: There are also 2 RW portions of the firmware, A and B, where A is used as the primary and B as the backup (both are verified.)
The image shows that verified boot is expected to be able to detect unexpected changes in RW firmware, and system boot file system changes, is does not however, check for changes in user data, because user data inherently needs to be able to change. And, as I said before, each time you boot up your Chromebook (doesn’t work when waking from sleep) this verification process happens, with little noticeable impact on start-up time since everything is done on the fly.
After using a Chromebook it can get reaaally annoying waiting for a windows laptop to start :P
Verified boot is not, however, the be-all end-all of security solutions. If a determined attacker were to get local access, they could bypass this by replacing the firmware, or enabling the write pin and then booting off of an external boot device. An attacker could also create a malicious browser plugin to track usage.
With that said, I’d like to refer to one of the “Guiding Principles” of Chrome OS as stated in their design docs.
The perfect is the enemy of the good.
Learn more about verified boot:
- https://www.chromium.org/chromium-os/chromiumos-design-docs/firmware-boot-and-recovery
- https://www.chromium.org/chromium-os/chromiumos-design-docs/verified-boot
- https://www.youtube.com/watch?v=WY2sWpuda2g
Small Attack Surface
I’ll keep this one short. Simply put, there’s much less you can screw up on Chrome OS than on something like Windows.
Sandboxing
If you aren’t familiar with the concept of sandboxing, it essentially means that all programs are contained to their own separate environment. When they are contained this way, programs (ideally) can only interact with the things that they should have access to, and nothing else.
In Chrome OS, everything is heavily sandboxed, each tab, and program* is run in it’s own process, so if you browse to a malicious website, or open something you shouldn’t have, it should not be able to escape the sandbox.
To do this, Chrome OS gives each process its own separate user id, and then uses Minjail to restrict access to things that a process doesn’t need, and grant what it what it does need with a policy list.
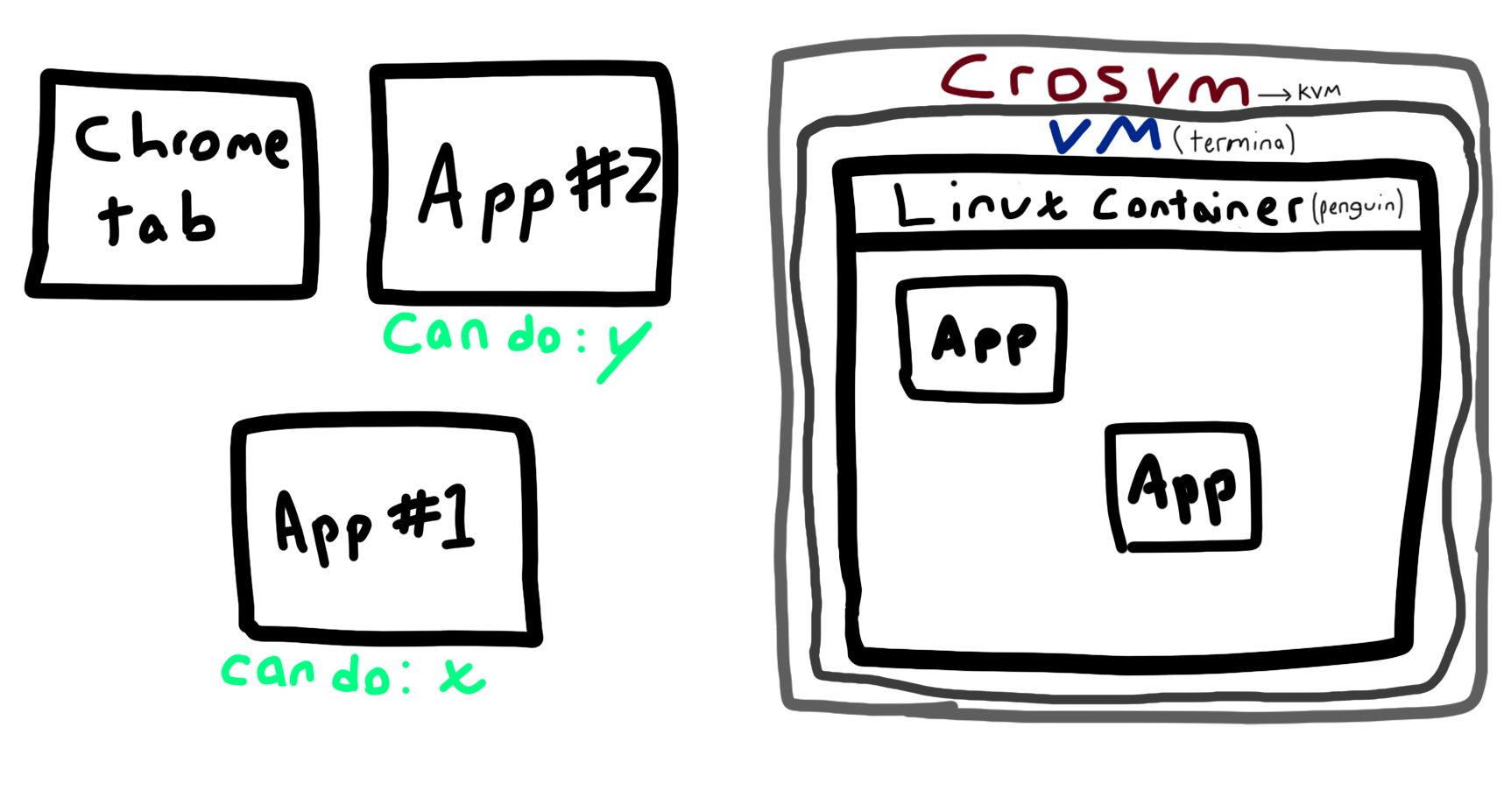
I’m not an artist don’t judge
Crostini (Linux on Chrome OS) is all run in a single container in the Termina VM. Which means that if you get something infected in Termina it can interact with the other apps in the Linux environment, but not outside of it. The Linux container can only interact with Chrome OS through the virtual machine manager “crosvm” which works with KVM (hats off to Google for using Rust to write a lot of this stuff btw :D)
BUT… you can manually create multiple VMs! Or if your hardware doesn’t permit that you can create multiple containers within the default VM. Check out this post on reddit for a how-to guide.
Learn more about sandboxing in Chrome OS:
- https://chromium.googlesource.com/chromiumos/docs/+/master/containers_and_vms.md
- https://events.google.com/io/schedule/events/d69f6bcf-3596-40e4-8fb1-7d5614402bbf
- https://prilik.com/blog/2019/05/16/crosvm-paravirt.html
Storage
While this might be a con for some, Chrome OS and Chromebooks are designed in a way so that pretty much everything goes on the cloud. This means that if something happens to your device, all you do is sign onto another one and everything (including things like your wallpaper) is how you left it. Since you sign into your Google account to get your online data, cloud storage is protected through Google, but local storage is another concern.
Each users data is encrypted separately through “vaults”, which hash and salt the username to create the directory, and then mount with eCryptfs. The user’s generated keyset (128 bit AES keys with additional entropy from the TPM, stored in kernel memory) is used to decrypt and encrypt the vault.
Automatic Updates
Chromebooks are automatically updated with little to no annoyance, however this will only last for 6.5 years from when the first device on the hardware platform is released. For some people, this could be a deal-breaker by itself.
Personally, I generally don’t keep devices for that long so it’s not too much of an annoyance to me. If you do buy a older Chromebook, though, that date could creep up on you faster than expected, and in turn make your device much less secure.
(The integrity of each update is checked by verified boot)
You can find more about this policy and a list of devices with their “expiration date” here
The Future of Chromebooks and Gaming?

Stadia logo owned by Google
It’s no secret that gaming capability on Chromebooks is pretty much non-existent. Weak hardware, paired with lack of support means you’re not exactly going to be hitting 300 fps on PUBG, if you could somehow get it installed in the first place.
“But wait! What about using Proton, since Chromebooks can support Linux?”
Well, there’s only GPU support for very few select devices (has to be enabled with a flag), and even if there was, the previously mentioned weak hardware would still be a major bottleneck. And let’s not forget, you’d be running a game inside of a container inside of a VM. Not ideal.
However, there could potentially be a savior… Stadia.
Stadia is essentially a cloud-based gaming service that lets you run demanding games on extremely low spec hardware, assuming you have a decent internet connection (>10mb/s recommended minimum). It’s expected to be released in November (A bit over a month away from time of writing)
This seems almost perfect for the situation that many Chromebook users could be in, and provided it actually works well, may be a great solution.
At the E3 Demo, Stadia was shown to perform exceptionally, which bodes well for the future.
Closing Notes
If you couldn’t tell by now, I’m a pretty big fan of Chromebooks. I believe they have a lot of potential outside of what they currently do, and am liking the direction that Google is taking them in.
If you’ve gotten this far, thanks for reading and hopefully I’ve convinced you to either give Chromebooks another try, or to continue using them :P